-Outline
-Research
-Executive Summary,
Intro
Threats and Mitigation Strategies
Conclusion
CASE STUDY
Talley Medical Surgical Eyecare Associates, PC May 2019 Unauthorized Access/Disclosure Breach
1. Conduct research to capture the organization’s infrastructure and processes, the threats to personal health information (PHI) and determine a strategy to mitigate the threats you anticipate. This research will go into the technical report (or white paper, nine to 10 pages excluding cover sheet, references, and any appendices) in accordance with the directions in Steps 5. After the paper is written, you will create a one-page executive summary of the paper. It will be part of the technical report document, immediately after the cover sheet and before the text of the report.
Step 5:- Develop Analysis of Threats to the Organization’s Information Systems Infrastructure
Topics to Address in the Description of Threats and Mitigation Strategies
2. Describe potential threats to the organization’s critical mission areas. These may include sloppy information security practices, insider threats, or hackers wishing to steal personal data. Relate these threats to the vulnerabilities in the CIA triad.
3. Describe how the organization restricts access to protect billing and PHI. Explain the organization’s processes and workflows to safeguard PHI, specifically the use of passwords, password management, and password protection in an identity management system.
4. Define the access management system. What types of access control management, to include access control lists in operating systems, role-based access controls, files, and database access controls will it take to ensure that access is limited to those with a need to know?
5. Define factor authentication systems. How do common factor authentication mechanisms, to include multifactor authentication practices, safeguard sensitive information for an organization like this?
6. Discuss strategic considerations and provide recommendations. Review the mission and organization structure of your organization as well as roles within the organization, and recommend accesses, restrictions, and conditions for each role
7. Discuss the manager’s risk considerations. What will happen if the CIO and the leaders do nothing and decide to accept the risks? Could the CIO transfer, mitigate, or eliminate the risks? What are the projected costs to address the risks?
The deliverables for this project include:
1. Technical report: A nine- to 10-page double-spaced Word document with citations in APA format. The page count does not include the cover sheet, executive summary, figures, diagrams, tables, or the references section.
2. Executive summary: This will be a single double-spaced page, and in the same document as the technical report, located immediately following the cover sheet and before the text of the report.
Professional homework help features
Our Experience
However the complexity of your assignment, we have the right professionals to carry out your specific task. ACME homework is a company that does homework help writing services for students who need homework help. We only hire super-skilled academic experts to write your projects. Our years of experience allows us to provide students with homework writing, editing & proofreading services.
Free Features
Free revision policy
$10Free bibliography & reference
$8Free title page
$8Free formatting
$8How our professional homework help writing services work
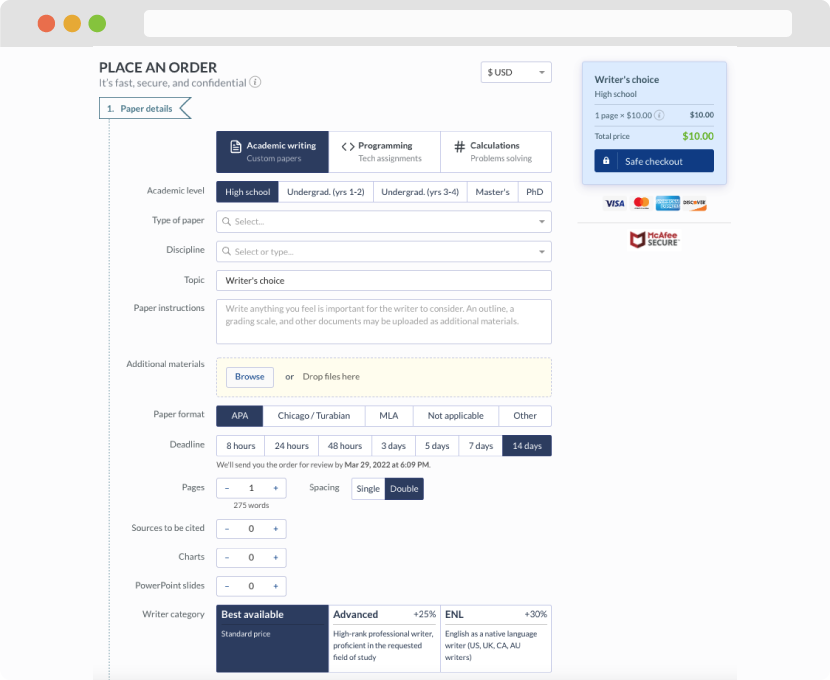
You first have to fill in an order form. In case you need any clarifications regarding the form, feel free to reach out for further guidance. To fill in the form, include basic informaion regarding your order that is topic, subject, number of pages required as well as any other relevant information that will be of help.
Complete the order form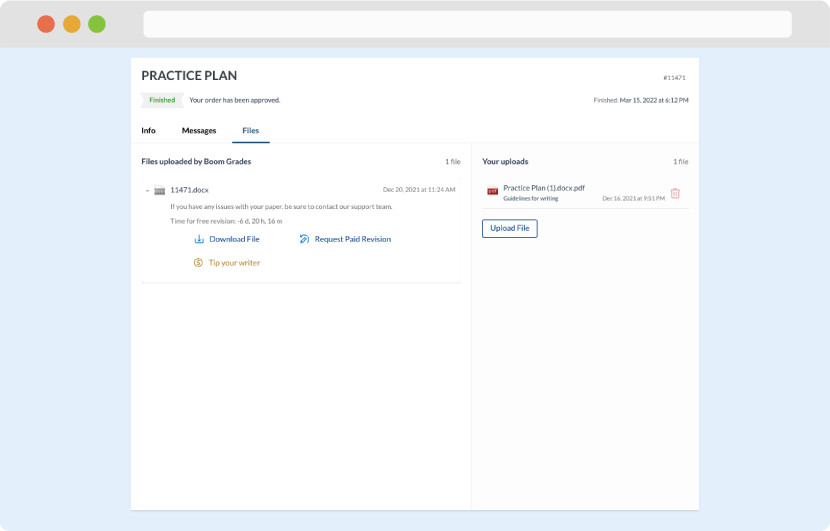
Once we have all the information and instructions that we need, we select the most suitable writer for your assignment. While everything seems to be clear, the writer, who has complete knowledge of the subject, may need clarification from you. It is at that point that you would receive a call or email from us.
Writer’s assignment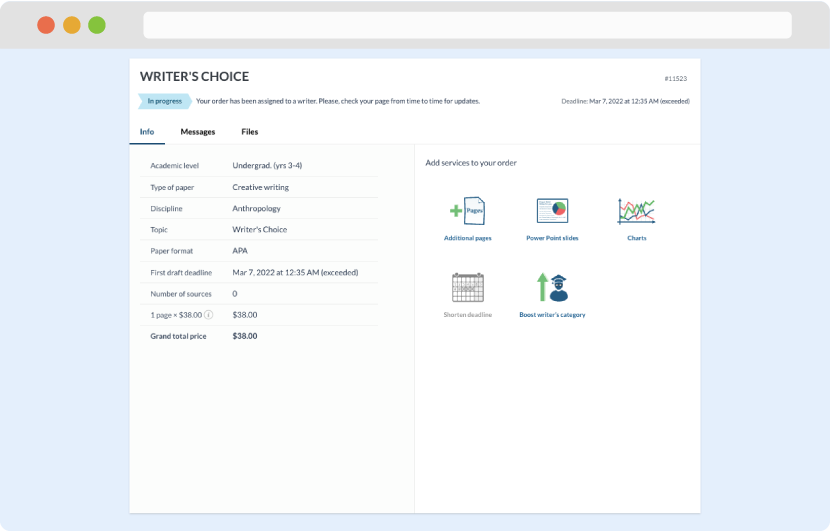
As soon as the writer has finished, it will be delivered both to the website and to your email address so that you will not miss it. If your deadline is close at hand, we will place a call to you to make sure that you receive the paper on time.
Completing the order and download